What if your security tools could see exactly what your applications do at runtime, catching threats the moment they occur? The Falco project has been doing precisely that for Kubernetes environments for the past decade.
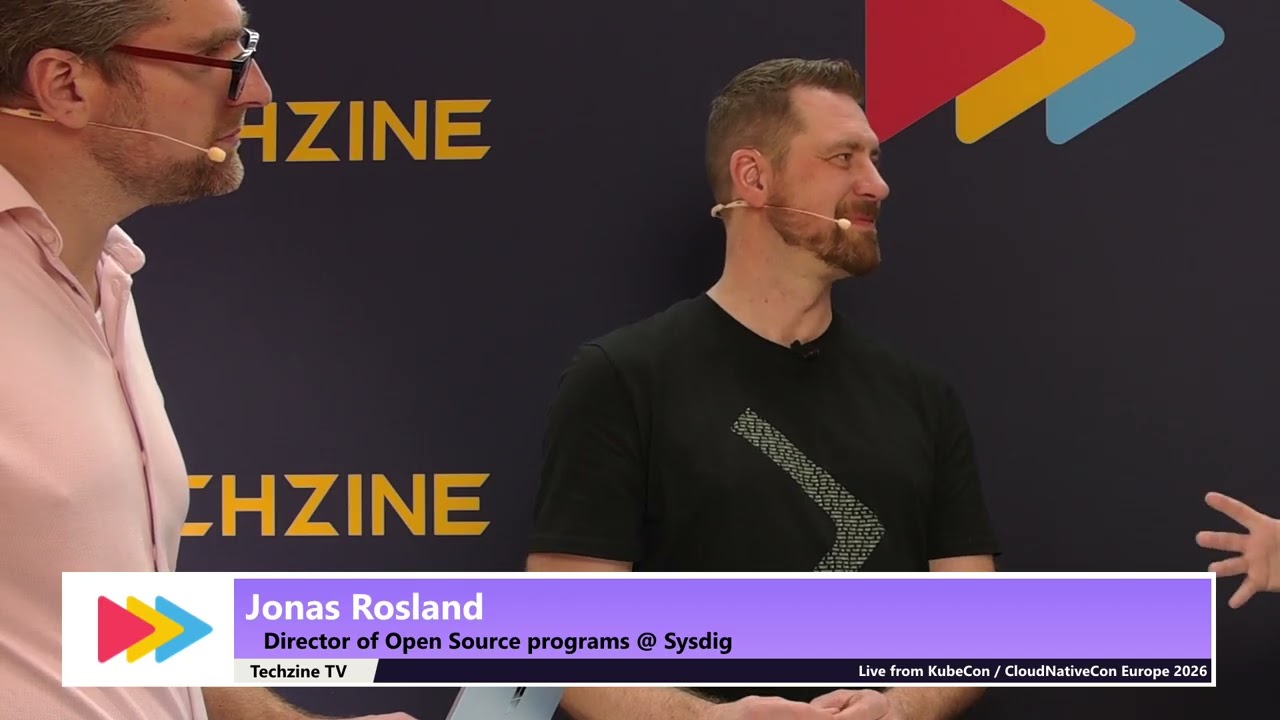
In this exclusive Techzine TV interview from Kubecon and CloudNativeCon, Jonas Rosland from Sysdig reveals how runtime security detection works differently from traditional static analysis, and why that difference could be critical for your organization’s security posture.
The conversation offers fascinating insights into modern attack vectors you won’t want to miss. Learn how a simple login delay led to discovering one of the most dangerous backdoor attempts in recent history, and why that vulnerability could only be caught through runtime monitoring.
What you’ll discover in this interview
Rosland doesn’t just explain what Falco does; he walks through real-world scenarios that demonstrate why runtime security has become essential. You’ll hear about the kinds of suspicious behaviors Falco detects, from unauthorized network connections to encrypted file downloads, and understand how these detections provide actionable intelligence to security teams.
The discussion takes an unexpected turn into the world of AI-generated code and the new security challenges it creates. Rosland shares a compelling demonstration of Falco blocking a malicious action attempted through an AI coding agent, even after the AI initially refused, and the developer claimed to have permission. This scenario reveals a critical security layer that most organizations haven’t considered yet.
Supply chain attacks and the dependency problem
If you think your organization understands its software supply chain, this interview might change your perspective. Rosland explains how supply chain attacks have evolved and why knowing your dependencies has become crucial. The real-world examples he provides illustrate just how far attackers will go to compromise systems.
You’ll learn why both runtime security and static analysis are necessary, how they complement each other, and what gaps exist when you rely on only one approach. The technical explanations remain accessible while providing depth that security professionals will appreciate.
Building security communities beyond code
There’s an unexpected angle to this conversation that extends beyond pure security technology. Rosland discusses how healthy open source security projects require more than just developers, and why non-code contributions from technical writers, video creators, and community builders are just as valuable for the project’s success.
This perspective offers insights for anyone involved in open source projects or considering contributing to security tools. The approach to community building that Rossland describes could apply to projects far beyond Falco.
Key topics explored:
- How runtime detection catches threats that escape static analysis
- Real examples of supply chain attacks and how they were discovered
- The emerging security challenges from AI coding assistants
- Why understanding your complete dependency chain matters
- Sysdig’s new capabilities for protecting AI workloads
- How Falco has evolved over its 10-year history
- The role of non-code contributors in security projects
Whether you’re responsible for Kubernetes security, interested in runtime detection capabilities, or trying to understand the new threat landscape created by AI-generated code, this interview provides perspectives you won’t find in typical security discussions. Watch the full conversation to understand why runtime security has become non-negotiable for cloud native environments.